In the realm of networking, the intricate dance of data transmission and reception is orchestrated by various configurations, among which Switchport Access Mode and Trunk Mode reign supreme. These pivotal settings determine how data flows between devices and networks, profoundly influencing the efficiency, security, and scope of communication within an infrastructure. Let’s delve into the stark differences and nuanced functionalities of these two indispensable modes to unravel their roles in shaping the modern network landscape.
Understanding Switchport Access Mode
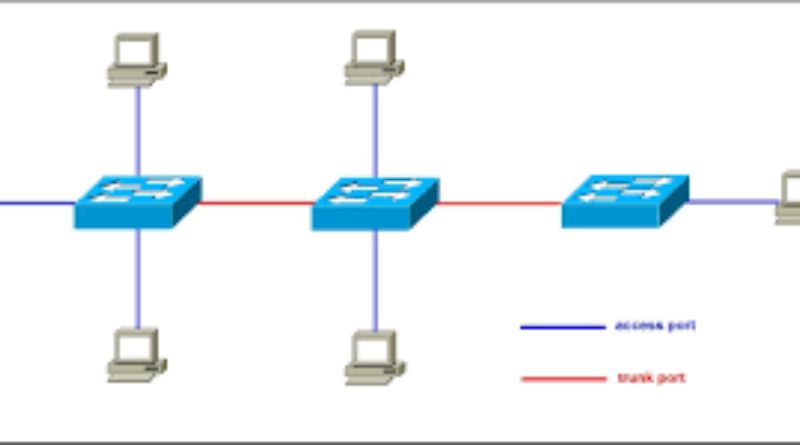
Switchport Access Mode serves as the gateway connecting end devices—computers, printers, or servers—to a switch within a network. Its primary function lies in segmenting and channeling traffic by confining it to a designated Virtual Local Area Network (VLAN). When a port is configured in Access Mode, it operates within a single VLAN, limiting communication to devices belonging to that specific VLAN. This setup facilitates streamlined communication among devices while keeping the traffic segregated from other VLANs, thus preserving network integrity and security.
In Access Mode, the switch strips away VLAN information from incoming data frames, relegating them to the predefined VLAN. By doing so, it creates a controlled environment where devices within the same VLAN communicate seamlessly, yet are shielded from interactions with devices in other VLANs.
The Essence of Trunk Mode
Contrary to Access Mode’s localized functionality, Trunk Mode assumes a more expansive role in interconnecting switches and facilitating the exchange of multiple VLANs across a singular connection. The port configured in Trunk Mode acts as a high-speed conduit for carrying data from various VLANs, enabling the seamless transmission of traffic between switches. This mode plays a pivotal role in ensuring the fluidity and efficiency of data flow across an expansive network.
Trunk Mode employs specialized protocols like IEEE 802.1Q or Inter-Switch Link (ISL) to encapsulate Ethernet frames with VLAN information. Through this process, these ports tag the frames with the relevant VLAN information, ensuring that when data traverses between switches, it reaches the appropriate VLANs, maintaining the integrity of the VLAN structure.
Distinguishing Features
Traffic Segmentation and Handling
The fundamental disparity between Switchport Access Mode and Trunk Mode lies in their approach to traffic segmentation and handling. Access Mode isolates and restricts traffic to a single VLAN, ensuring that devices connected to the port communicate solely within that VLAN. Trunk Mode, on the other hand, operates on a grander scale, allowing the passage of multiple VLAN traffic across switches, promoting inter-VLAN communication.
End Device vs. Switch Connection
Access Mode primarily caters to connecting end devices to a switch, whereas Trunk Mode functions as the conduit between switches. Access Mode ensures devices operate within a specific VLAN, while Trunk Mode ensures multiple VLANs communicate harmoniously across switches, contributing to the holistic functioning of the network.
VLAN Tagging
Another critical distinction between these modes is their treatment of VLAN information. Access Mode strips VLAN information from frames, simplifying communication within a single VLAN. In contrast, Trunk Mode retains and utilizes VLAN tagging, marking frames with specific VLAN information to facilitate accurate routing of traffic across switches.
Optimal Use Cases
Selecting the appropriate mode is contingent upon the specific requirements and architecture of the network in question. Access Mode finds its niche in smaller, more straightforward networks or for connecting individual devices, where segregation of VLANs is essential to maintain network organization and security. On the other hand, Trunk Mode is indispensable in larger, complex networks where multiple VLANs need to coalesce and communicate efficiently across switches.
Misconfiguration of these modes can lead to a multitude of issues, from connectivity problems due to VLAN mismatches to potential security vulnerabilities caused by unauthorized access to sensitive data residing on different VLANs. Therefore, proper configuration and implementation of these modes are pivotal for the smooth functioning and security of a network.
Real-world Applications
In real-world scenarios, the significance of Access Mode and Trunk Mode manifests in various network setups, each leveraging their functionalities to optimize communication and security.
For instance, in a corporate environment, Access Mode would be utilized to link individual devices—computers, printers, or VoIP phones—to the corporate network, ensuring that departments or teams can communicate internally while staying segregated from other segments of the network. This segregation enhances security, reducing the risk of unauthorized access to sensitive data.
On the flip side, Trunk Mode comes into play when interconnecting switches within the corporate network. In this context, Trunk Mode allows the seamless transfer of data across different VLANs, aiding in the efficient exchange of information between various departments or office locations connected via multiple switches.
Troubleshooting and Best Practices
Configuring these modes demands a meticulous approach. Best practices include meticulous documentation, clearly defining VLAN assignments, and conducting regular audits to ensure that the settings align with the network’s requirements. Troubleshooting misconfigurations involves detailed analysis, including checking VLAN assignments, ensuring consistency across switches, and verifying that Trunk ports are correctly configured to handle multiple VLANs.
In conclusion, the juxtaposition of switchport Access Mode and Trunk Mode illustrates their pivotal roles in steering network traffic and communication. Their divergent functionalities cater to the diverse requirements of networks, from segmenting traffic within a VLAN to facilitating the exchange of data across switches. Appropriate configuration and comprehension of these modes are instrumental in sculpting a robust, secure, and efficient network infrastructure.